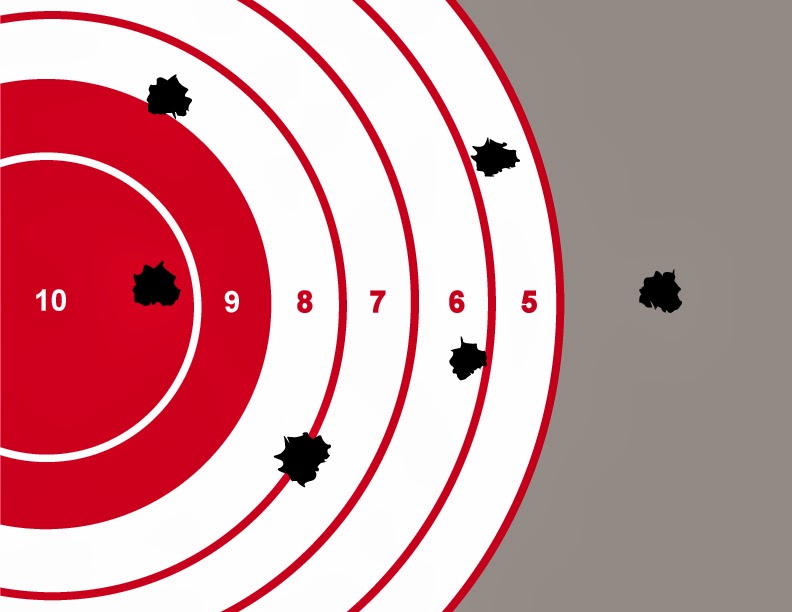
Assume that you are a Target
There has been a buzz in the Uplogix office about the much-publicized Target credit card information breach. No, not just because many of us are now carrying shiny new credit cards proactively replaced by our banks due to our vulnerability as frequent Targét (say it Tar-zhay) shoppers, but because initial reports indicated that the breach relied [...]