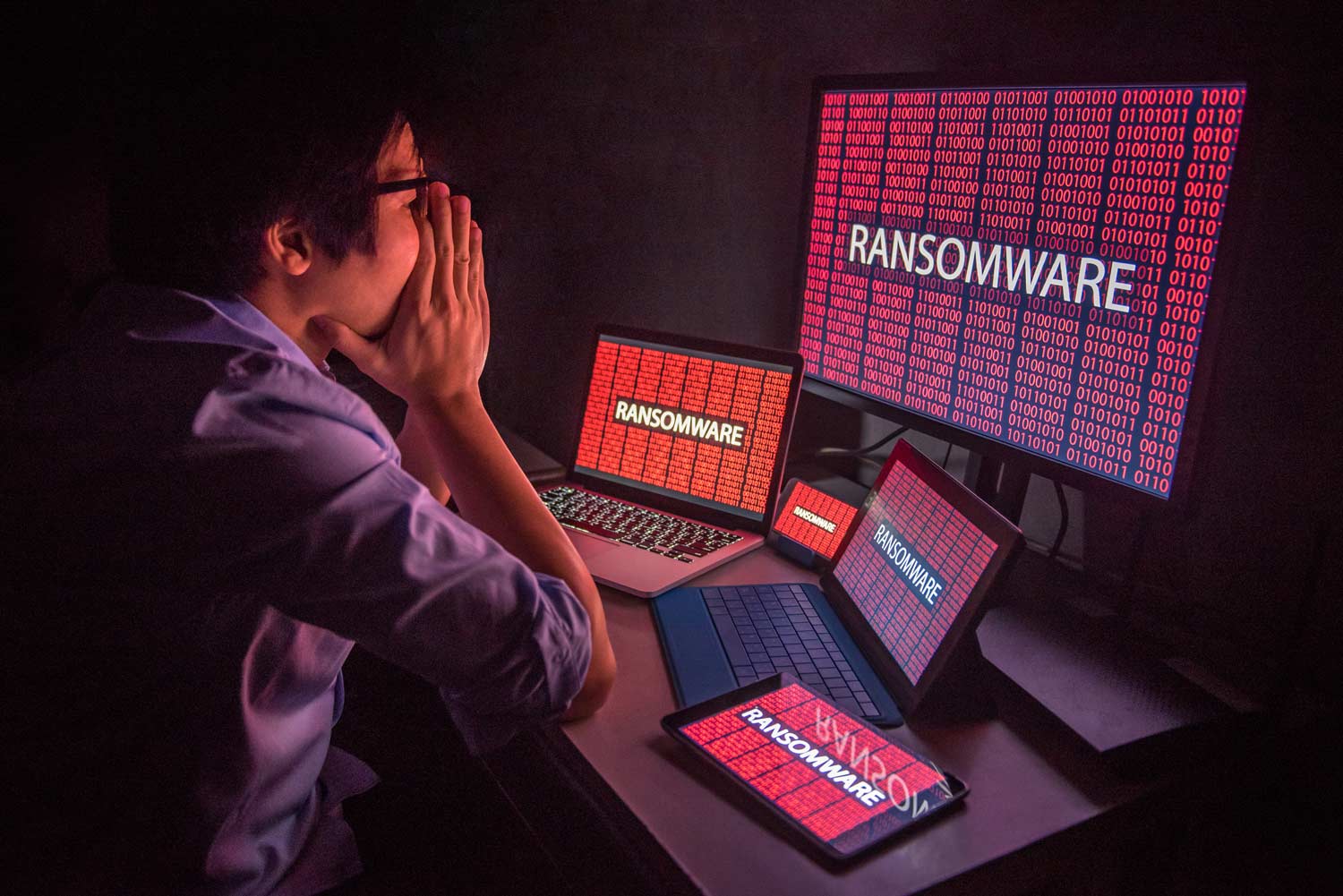
Montgomery County in Alabama was hit by a ransomware attack that left IT staff scrambling to regain control of their systems. Among other impacts, vehicle tags and registrations are unable to be processed as officials investigate the cause of the breach and their options to regain control and clean up their system.
The debilitating ransomware attack was confirmed Tuesday morning when administrators were locked out and a ransom was demanded, to be paid in bitcoin. The county was working with the FBI as well as security vendors including Akamai, Viper, Cisco and Microsoft.
This type of attack is increasingly common, driving prepared IT organizations to be ready for when they get a ransomware or other kind of attack. One option for recovering from a hack is the functionality of the Uplogix platform. You need a clear plan, or blueprint, for network recovery after the hack that doesn’t rely on the network itself or slow trips to remote sites for “sneaker net” repairs.
This blueprint for how you are going to recover your network infrastructure after a hack can reduce or mitigate the severe impacts of a breach. Impacts that go far beyond the steps you hear about on the news like customer notification and ongoing protection costs. Network recovery means stopping the immediate threat of compromised security by locking down the network or limiting functionality to specific areas, remediating security controls and addressing the disruption and continuity of business issues the event causes. Long term, it’s about fixing the gaps and dealing with regulatory, audit and compliance issues.
Uplogix has functionality that should be part of your blueprint, for both before and after the hack. We’ve put some highlights into an infographic.
Before the breach, you can move management of network infrastructure out-of-route. By configuring devices to only accept management traffic from Uplogix over the console port, these devices are locked down. Potentially malicious outside traffic aimed at changing configurations, powering down or other unauthorized changes are blocked. Access to Uplogix is highly secure, integrating with TACACS and Radius and incorporating a highly granular authorization system.
After the breach, Uplogix can operate independently of the network over its dedicated out-of-band connection. Continuous monitoring means quick alerting when there are issues and last-known or golden configurations can be pushed to devices, wiping out malicious changes. The secure out-of-band access ensures access even when the primary network is down or degraded.
Your blueprint can include configurations for a “safe mode” for network devices, limiting functionality to effectively quarantine sections of your network. With Uplogix you can push a config to one device, or thousands deployed across your network.
Finally, if it has really hit the fan, Uplogix can act as a backup cellular router by sharing its out-of-band LTE connection, providing a reliable failover network to keep critical traffic moving.
Be prepared with Uplogix and our Network Restoration Blueprint. From locking out the bad guys to deploying safe mode, the infographic highlights network recovery with out-of-band.